Completion of Zero Trust Architecture

Collect
It stores network traffic as they are without any loss of data on a maximum of the 40G network.

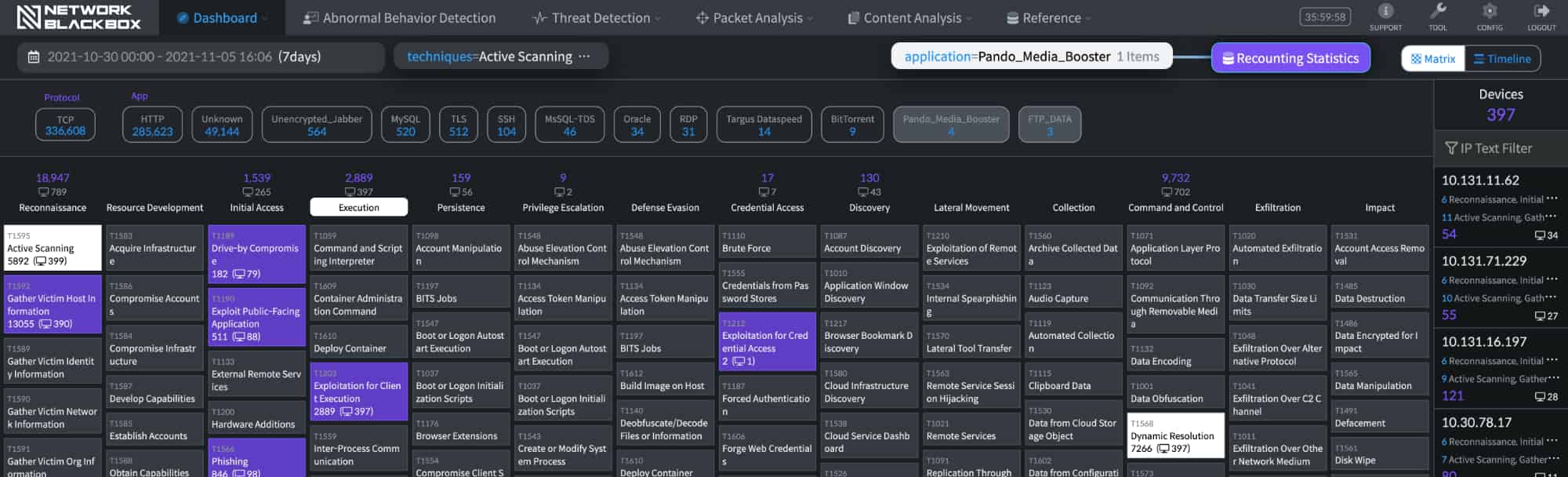
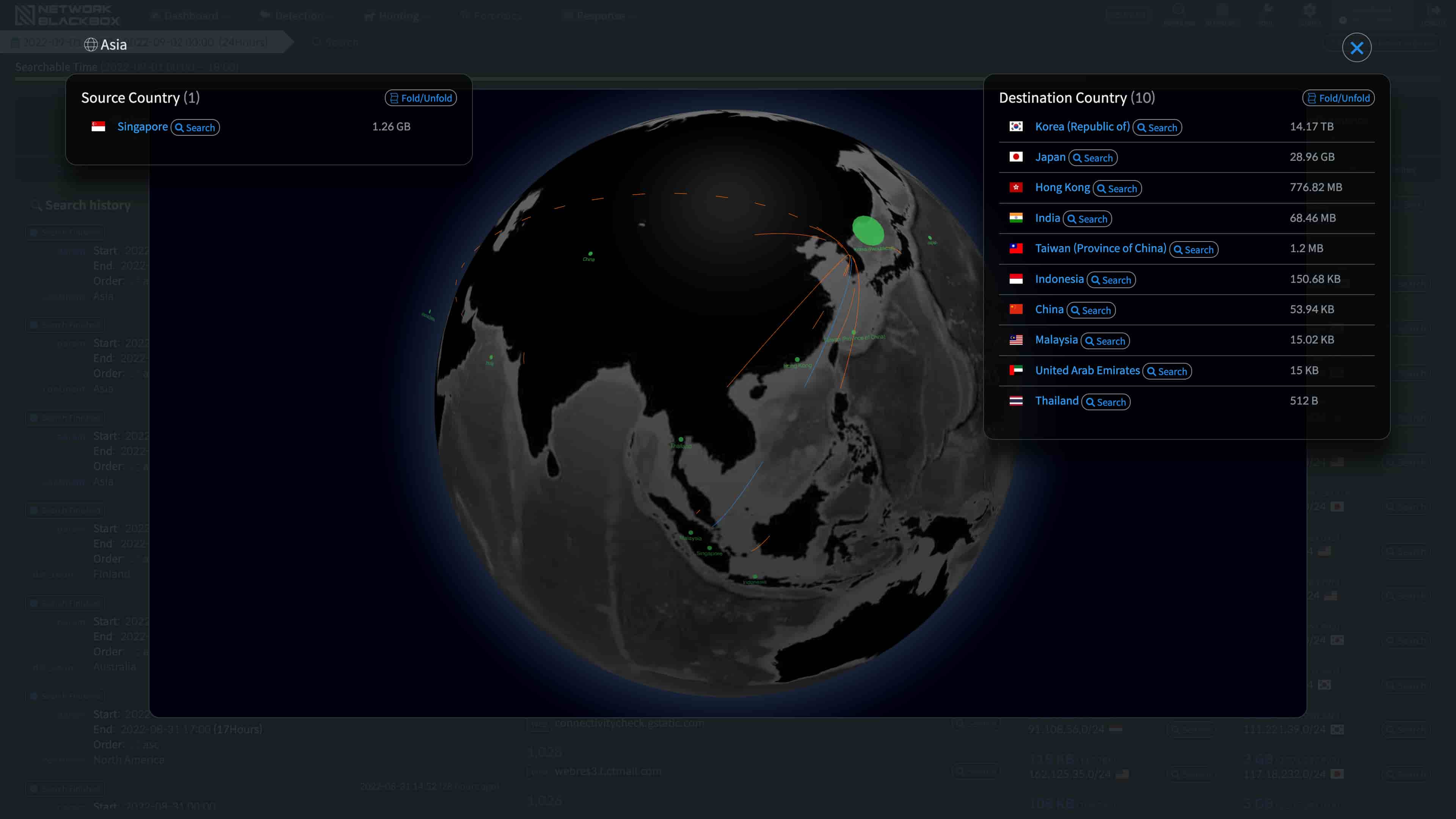
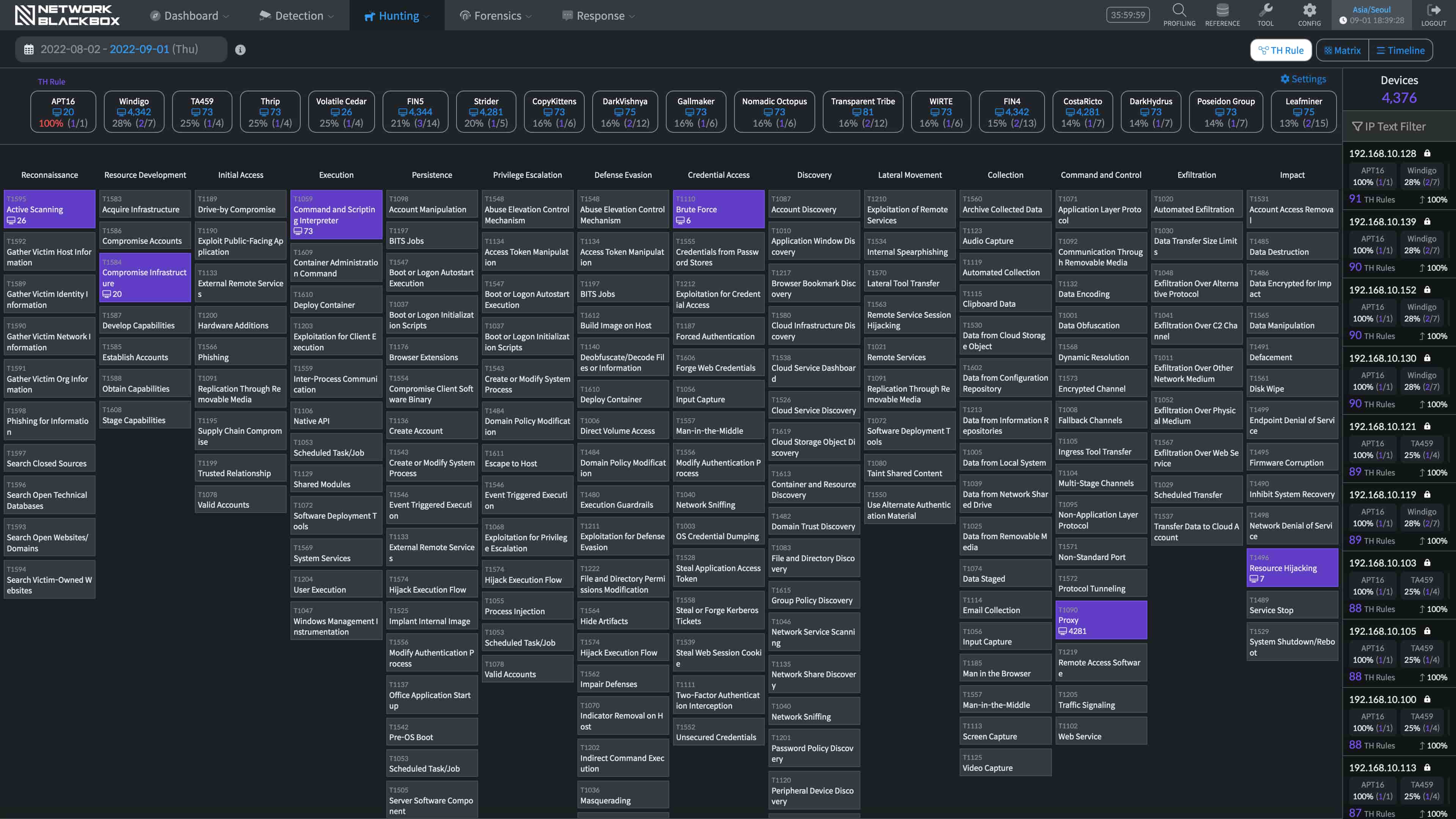
Hunting
Establish a framework from the TTPs perspective to hunt threats.

XSec
Provides evidence of specific attacks in an infringement accident.

Response
It informs you of the threat actions that have occurred through various channels.
100% Full Packet Capture
40Gbps
Connectivity
100%
Zero Packet Loss
Payload
Save up to 15PB
※ We collect packets using a mirroring method, while there is no impact to the network.
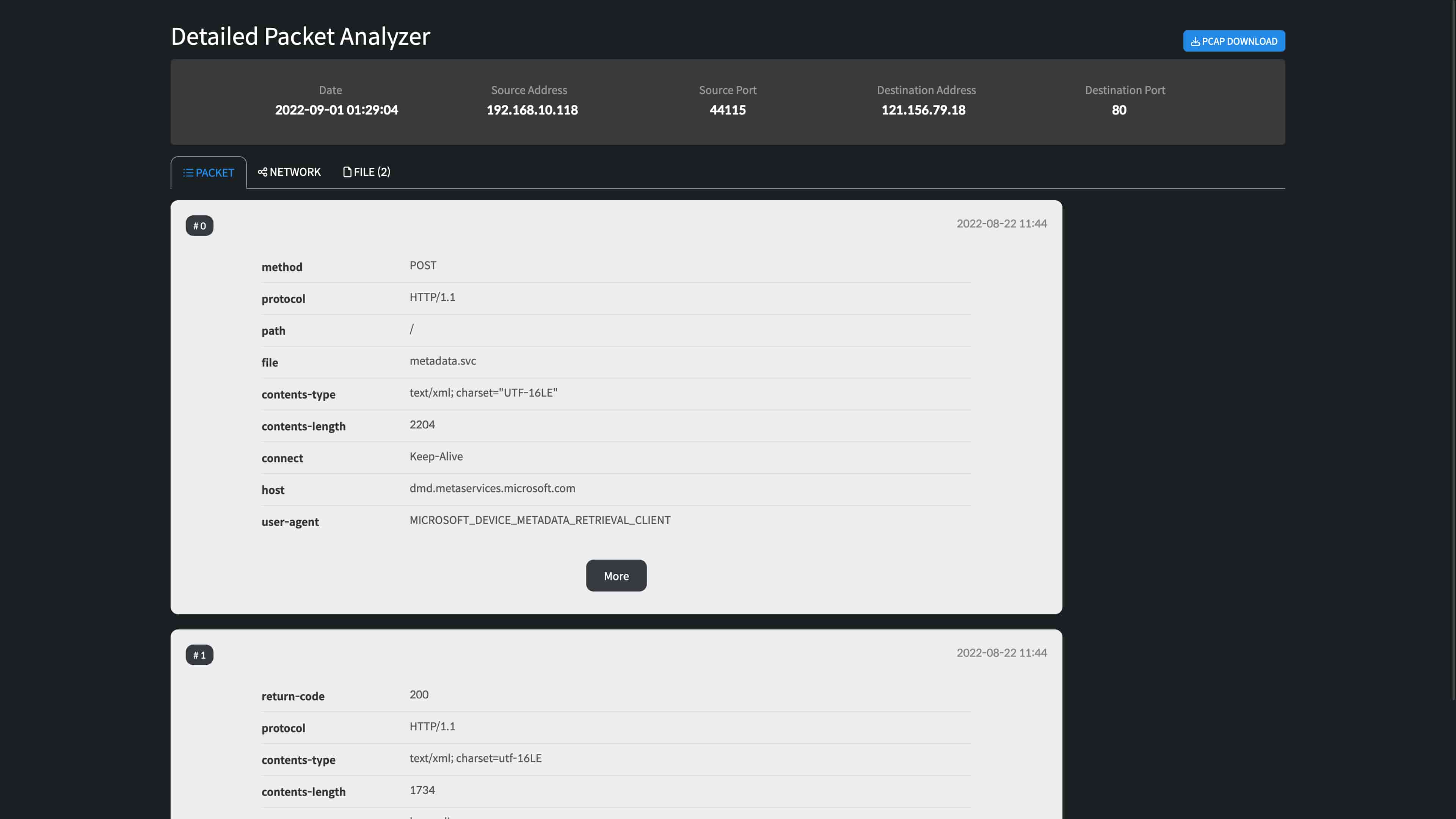
Recombining network packets in real time
It does not simply store packets,
but instead recombines up to the range of Application Layer (L7) to visualize what’s happening on the network.
※ In addition, it performs various post-processing tasks such as virus scan, detection of abnormal actions, and etc.
- Physical
- Data Link
- Network
- Transport
- Session
- Presentation
- Application
It visualizes traffic from all network layers.
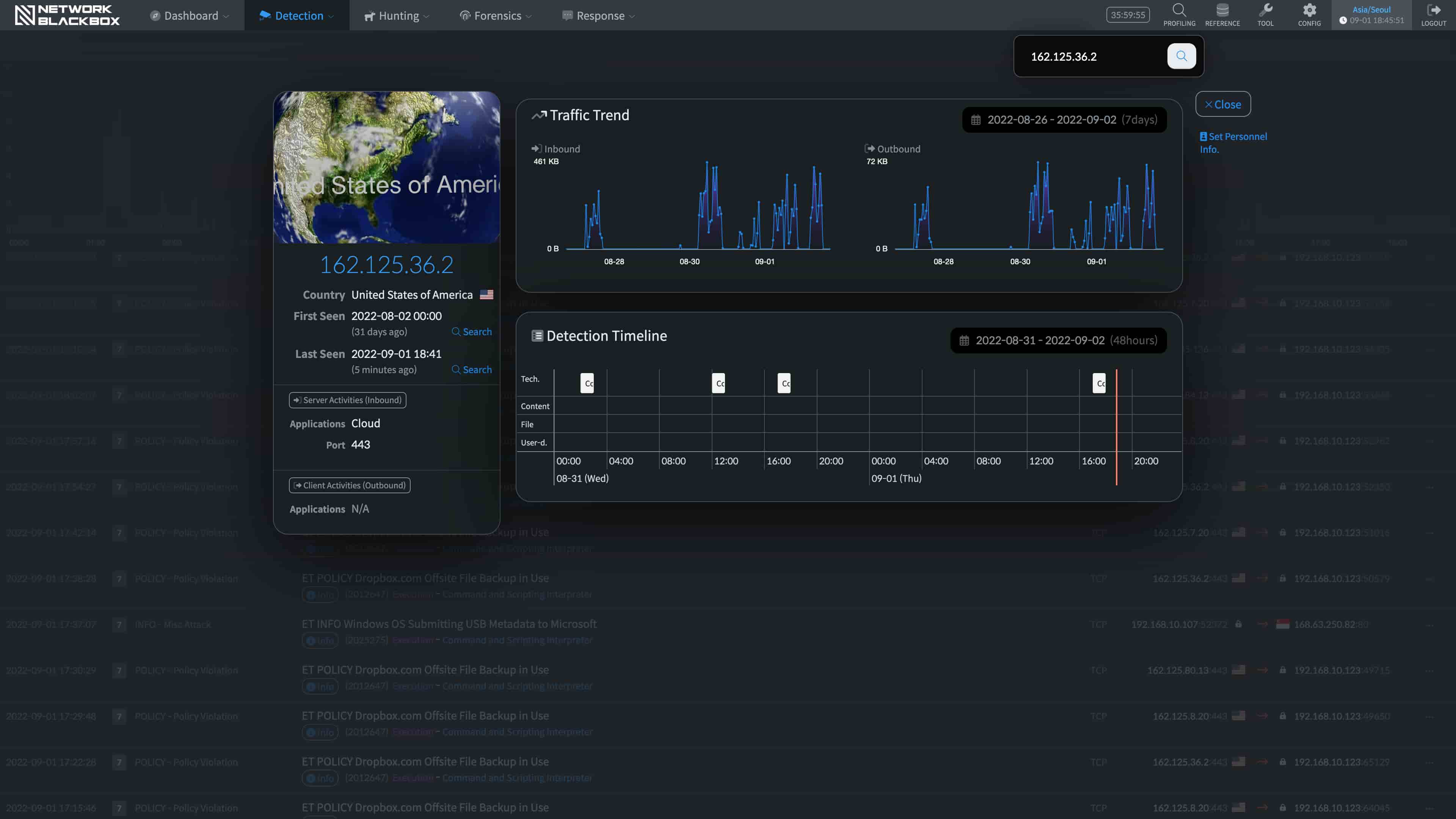
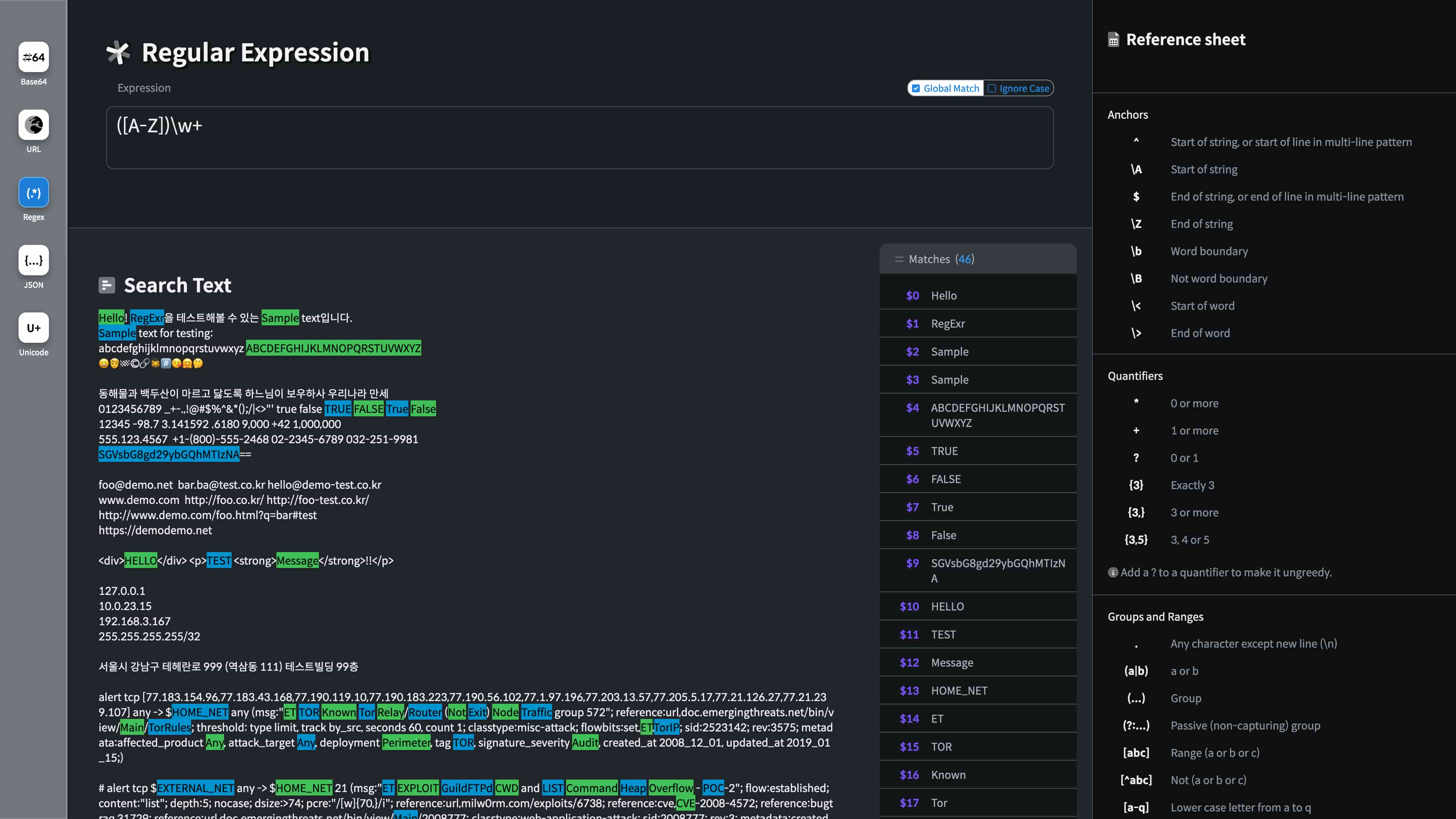
Real-time intelligent threat detection
It uses the newest threat detection rules to detect unusual signs in real time.
25000+
Cyber Threat Hunting
Realtime
Anomaly Detection
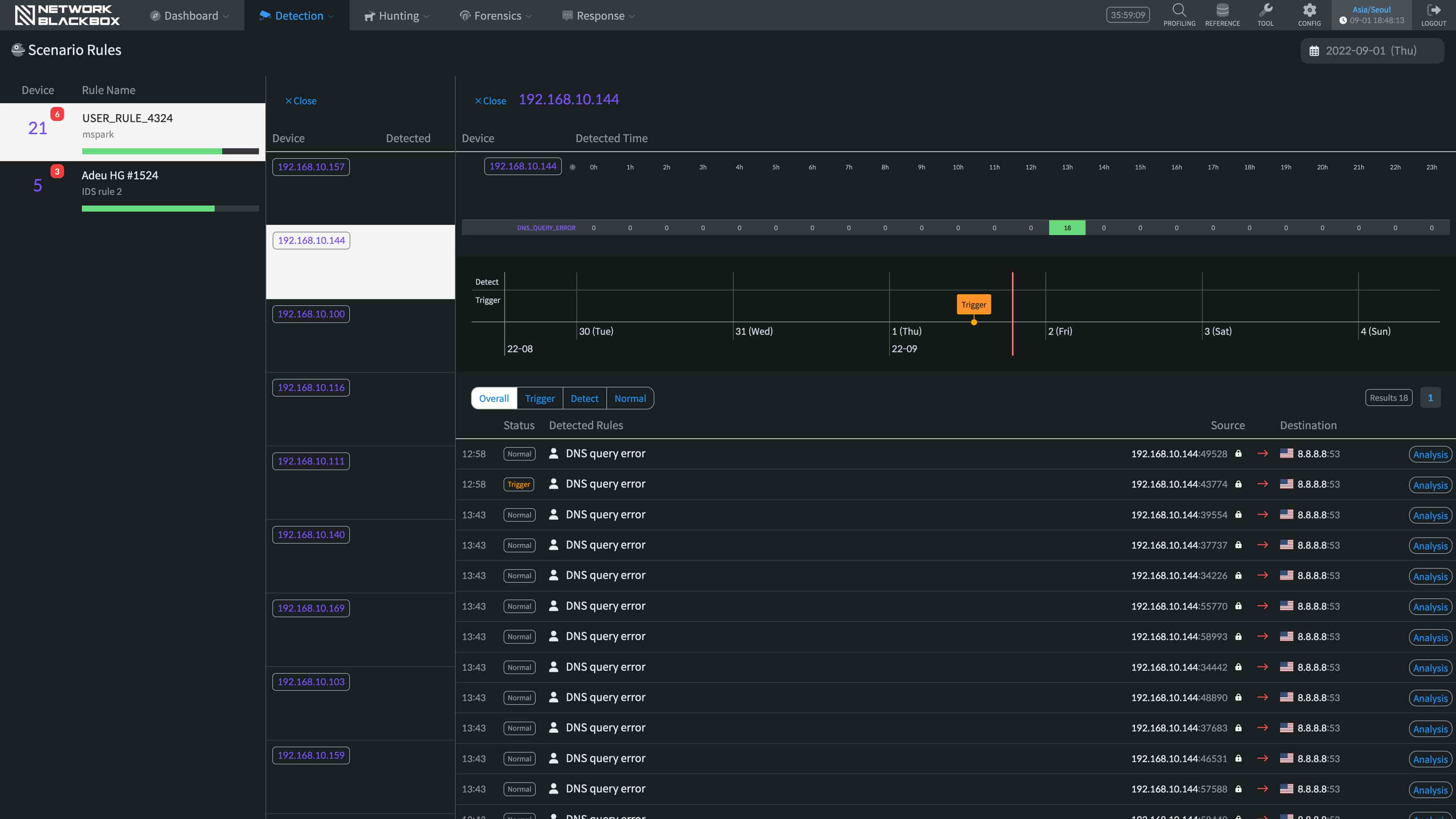
 Responding to highly sophisticated threats
Responding to highly sophisticated threats
Signature-based attack detection
Behavior-based attack detection
C&C, malware and worm detection
Scenario-based attack detection
It provides clear visibility malware by analyzing the detected details gathered from various angles.
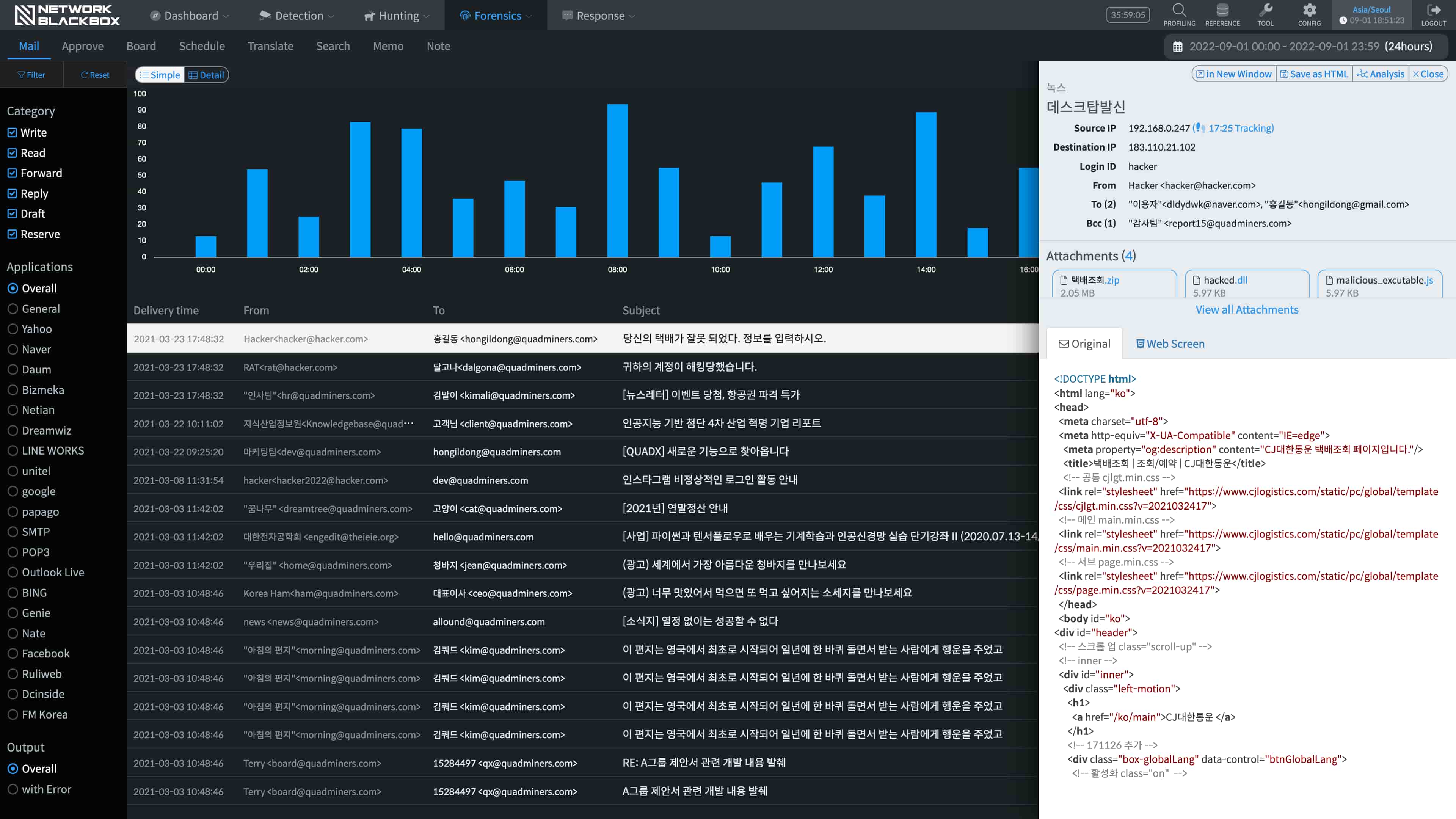
In-depth analysis of network traffic
More than simply analyzing for cyber threats, it checks the actual packets, not just logs, through its highly refined Database.
More than 20 variations of data analysis sets
| Payload | Flow | Contents | Rules | ... | ... |
Correlation analysis with more than 80 variations of conditions
| Stats | Event |
Threshold-based analysis
and analysis of events collected from multiple devices
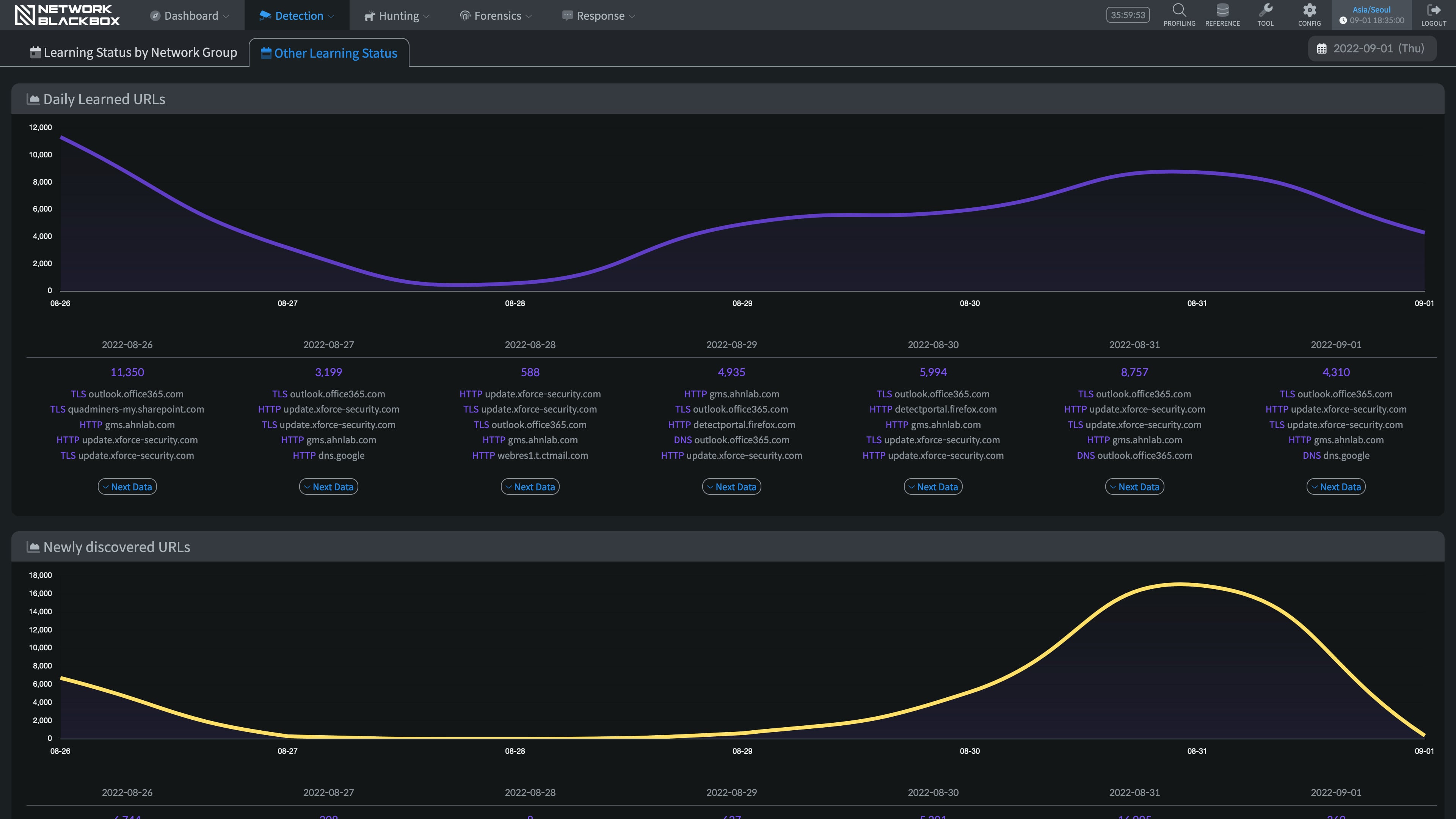
Machine Learning based AI Analysis Engine
It precisely runs detections by learning detected events as well as various behaviors that occur on the network. It is a machine learning based AI solution that is able to explain reasons and causes of the results.
- Flow
- Statistics
- Content
- Event
Algorithm
to highly
sophisticated
threats


Patent applications in South Korea
- A high-performance packet stream storage system and its method using the system (10–2080477)
- A pattern-based index processing system and its method using the system (10–2080478)
- A scenario-centered real-time attack detection system and its method using the system (10–2080479)
International patent application (PCT, United States of America, Japan)
- A network forensic system and its method using the system (PCT-KR2019-008860)
 GS Certification Level 1
GS Certification Level 1
Network Blackbox, a Cyber Threat Security solution has received GS Certified Level 1.
Network Blackbox 3.0
Certification Number 21-0562