Advanced Security
Discover a comprehensive defense against today’s cyberthreats
Advanced Security Datasheet
PDF, 0.9 MB
Acronis Active Protection technology
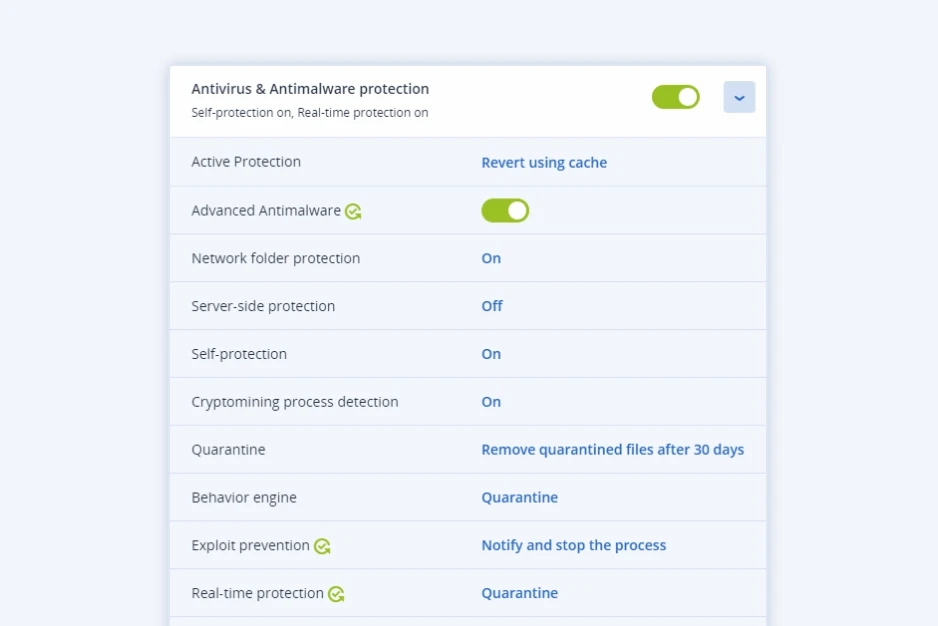
Acronis Active Protection technology, enhanced with exploit prevention, URL filtering, anti-ransomware and anti-malware detection for backed-up data and improved detection rates, catch more threats, faster.
Cyber Security automation
Smart, easy protection policy management, auto-allowlist custom apps, automatic malware scans and AV definitions updates as part of recovery process to deliver services more effortlessly.
Efficient forensics
Collect digital evidence and save it in a secure central repository to enable thorough post-incident investigations and proper remediation, while keeping costs down.
Built on AI-powered, next gen cyber protection
Minimize the risk for clients with Acronis Cyber Protect Cloud, the single cyber protection solution that integrates best-of-breed backup and recovery, endpoint protection management, and cybersecurity – with anti-malware technology that counters ransomware and zero-day attacks and complements your clients’ current antivirus. Enhance their protection with Advanced Security’s full-stack anti-malware – replacing their antivirus with our proven, integrated cyber protection.
| Features | Acronis Cyber Protect Cloud |
With Advanced Security |
|---|---|---|
| Next gen, behavior-based technology built to proactively stop cyberthreats, with a focus on ransomware and zero-day attacks | ||
| Vulnerability assessments | ||
| Data loss prevention (DLP) with device control | ||
| Backup and recovery | ||
| Automatic data recovery after a ransomware attack | ||
| Security gap identification with #CyberFit Score | ||
| Full-stack anti-malware protection: Real-time protection covering all attack vectors with multiple defense layers | ||
| URL filtering: Block malicious URLs, web-based attacks, and COVID-19 scams | ||
| Exploit prevention: Behavior-based detection heuristics prevent the exploitation of unknown vulnerabilities, including memory exploits and injections | ||
| Anti-malware scans of data in the Acronis Cloud: Offload client endpoints to enable more aggressive scans and ensure malware-free backups | ||
| Forensics data in backups: Collect digital evidence to faster and reduce the cost of remediation | ||
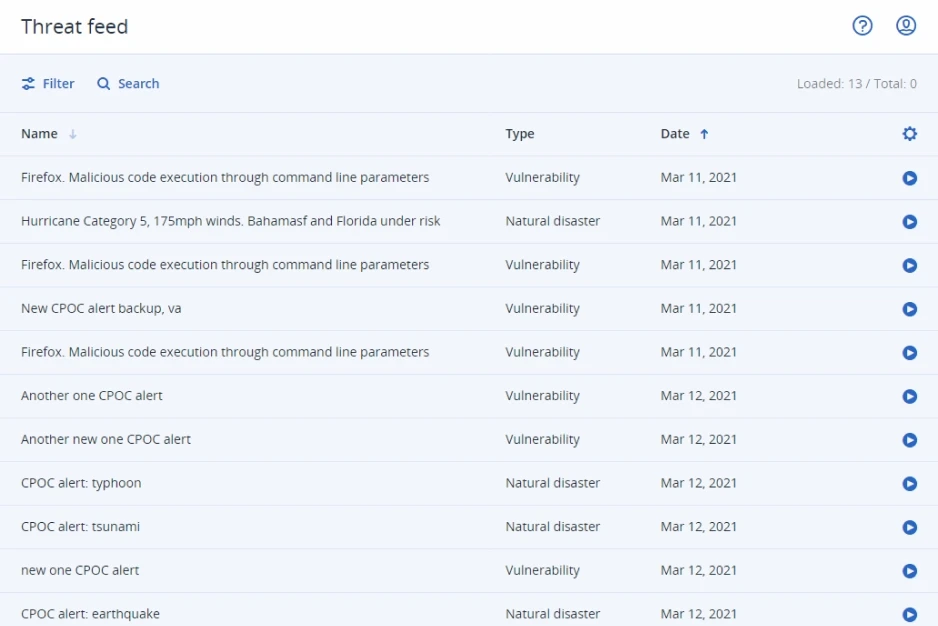
| CPOC threat feed: Increase reactiveness to emerging threats and get remediation suggestions | ||
| Automatic allowlisting: Reduce false positives and enable more aggressive scanning | ||
| Malware reinfection prevention: Scan for malware and update AV definitions during recovery to prevent a threat from reoccurring |
Enhance your cybersecurity services with advanced endpoint protection
Advanced Security enables you to offer more cybersecurity services with less management burden, replacing non-integrated antivirus tools with complete endpoint security that’s integrated with data protection.
Expand your services with advanced malware protection
Increase proficiency and minimize client risk with a full-stack anti-malware solution that covers more attack vectors, including the web and vulnerability exploits, with superior detection rates and prevention of threat recurrence that’s unique in the industry.
Improve your efficiency to save time and resources
Modernize your endpoint protection by replacing non-integrated antivirus with a single, integrated solution for thorough cyber protection. Cut costs through solution consolidation. Enable faster reaction time with security automation. Accelerate your detection speed, eliminate false positives, and reduce the load on client endpoints by scanning workloads for malware in the Acronis Cloud.
Enable complete, fast, and cost-effective remediation
Protect the recovery process to prevent threat recurrence. Ensure breaches are fully remediated with forensic insights. Ease the process and reduce the cost of security investigations by collecting digital evidence and forensic data in backups, where it’s protected against threats.
Full-stack, advanced malware protection
Replace non-integrated antivirus tools and protect clients with a single, integrated cyber protection solution that stops today’s sophisticated cyberthreats and ensures seamless remediation while eliminating the need to juggle multiple solutions.

Anti-malware technology
Leverage power AI-, signature-, and behavior-based detection and URL filtering to stop malware in real time.

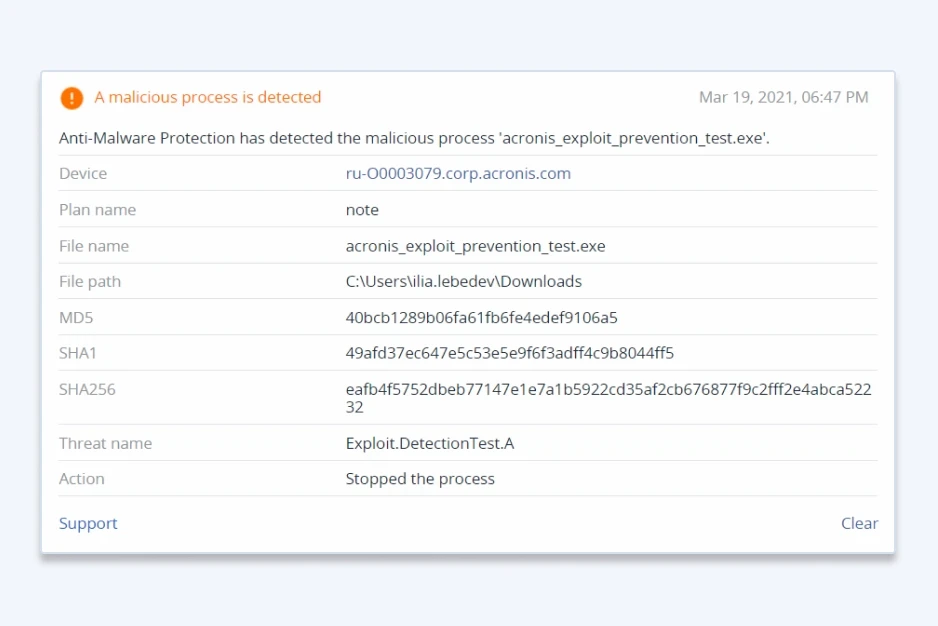
Exploit prevention
Prevent zero-day vulnerabilities and exploits, including memory exploits.

Protection of data in backups
Leverage more aggressive scans of backed up data in Acronis Cloud, reducing load on clients’ endpoints and ensuring recovery of clean data.
Stop modern cyberthreats with advanced endpoint protection
Full-stack anti-malware
Minimize the attack surface on client systems with enhanced anti-malware technologies. Improve the speed and accuracy of your detection rate with an upgraded set of malware signatures. Counter zero-day attacks and memory exploits in real-time. Scan backed-up data for malware.
Safe recovery
Prevent dangerous infections from reoccurring with Acronis’ unique safe recovery technology. During the recovery process, the integrated solution scans the backup for malware, installs the latest security patches, and updates its antivirus databases.
Forensics data in backups
Reduce the costs of maintaining compliance and running future incident investigations by collecting digital evidence – like memory dumps and process information – and storing them in a secure, central repository.
Smart protection plans
Acronis Cyber Protection Operation Centers (CPOCs) continuously monitor the cybersecurity landscape, releasing alerts on emerging threats such as malware, vulnerabilities, or natural disasters. Protection plans are automatically adjusted to proactively address those threats.
Expand your services with advanced protection packs
Add other powerful components to strengthen your services even further with advanced protection packs and unique cyber protection capabilities. Control your costs by paying only for the functionalities your clients need.
Advanced packs include:
Advanced Security
Enhance your security services with integrated cyber protection that includes full-stack anti-malware. Increase your detection rate and responsiveness to the latest cyberthreats. Extend cyber protection to web browsing, backed-up data, the recovery process, and exploit prevention. Enable investigations by capturing forensic data in backups.
- Full stack anti-malware
- URL filtering
- Exploit prevention
Advanced Backup
Defend clients’ data, even between scheduled backups. Extend backup capabilities to SAP HANA, Oracle DB, MariaDB, MySQL, and application clusters. You can also gain visibility into data-protection statuses across your clients’ infrastructure.
- Continuous data protection
- Data protection map
- Off-host data processing
Advanced Email Security
Block any email threat, including spam, phishing, business email compromise (BEC), advanced persistent threats (APTs), and zero-days in seconds before it reaches end-users. Leverage Perception Point’s next-generation technology for lightning-fast detection and easy deployment, configuration, and management.
- Anti-phishing and anti-spoofing engines
- Anti-evasion technologies
- Next-generation dynamic detection against zero-days