Features
Features
Acronis Cyber Protect Cloud
The best backup and recovery enhanced with essential endpoint protection capabilities and security management toolkit for centralized administration and monitoring.
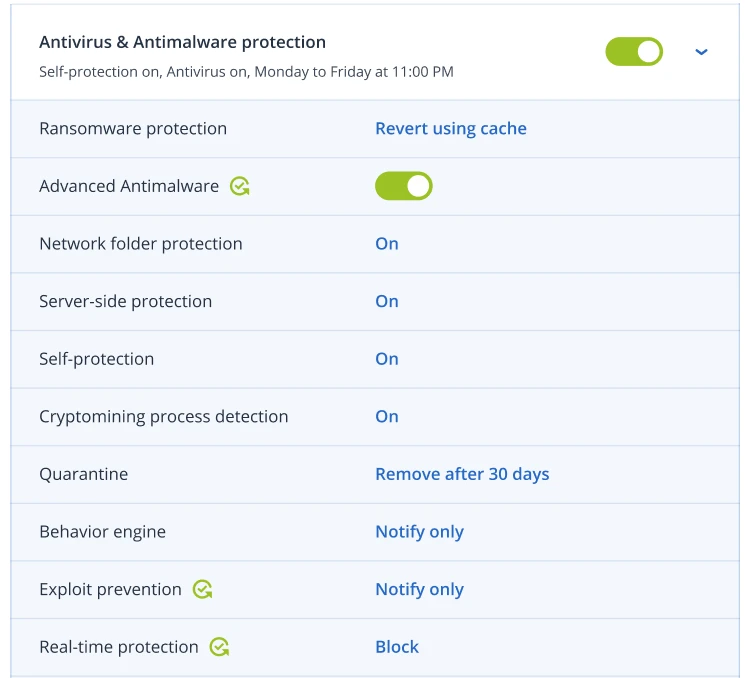
Acronis Active Protection technology
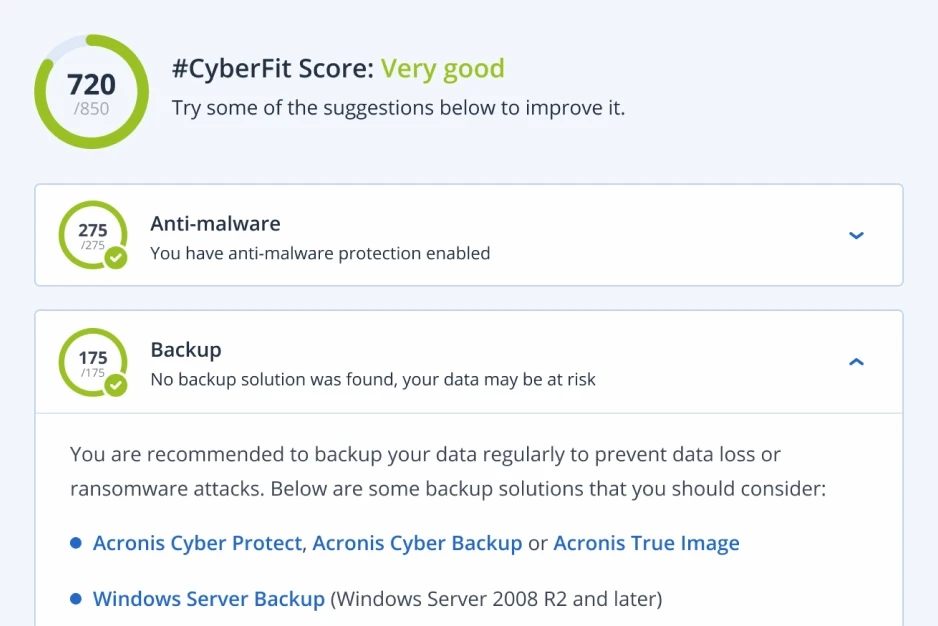
#CyberFit Score
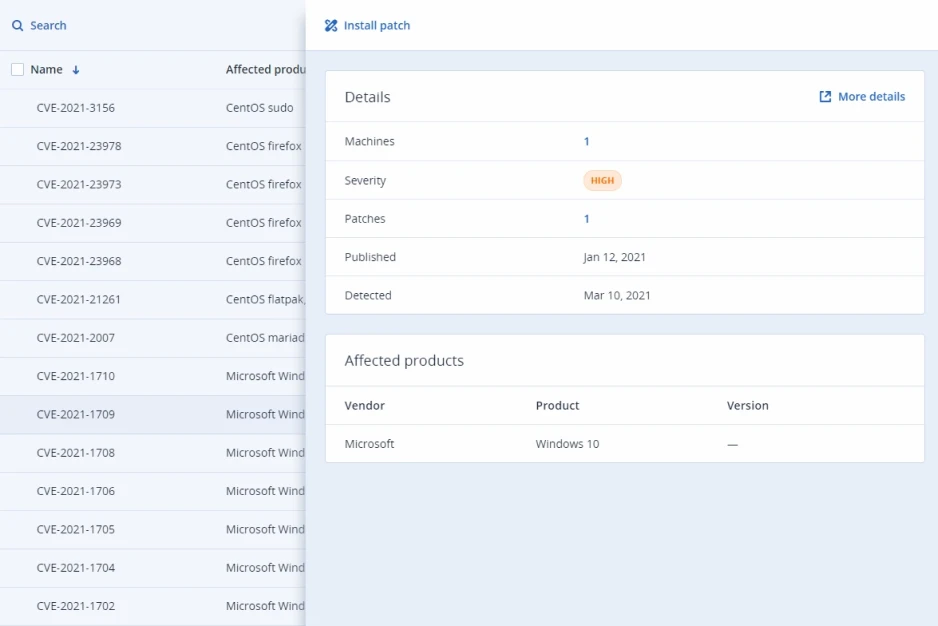
Vulnerability assessments
Identify and close the security gaps in your clients systems. You can scan client machines for vulnerabilities to ensure that all applications and operating systems are up-to-date and can’t be exploited by cybercriminals.
Protection for remote workers
Minimize the rising risk of cyberattacks for remote workers with multiple protection capabilities – including prioritized patching and protection for mission-critical telecommute apps (Zoom, WebEx, MS Teams, Slack, Skype, TeamViewer), remote device wipe, and secure desktop remote connectivity.
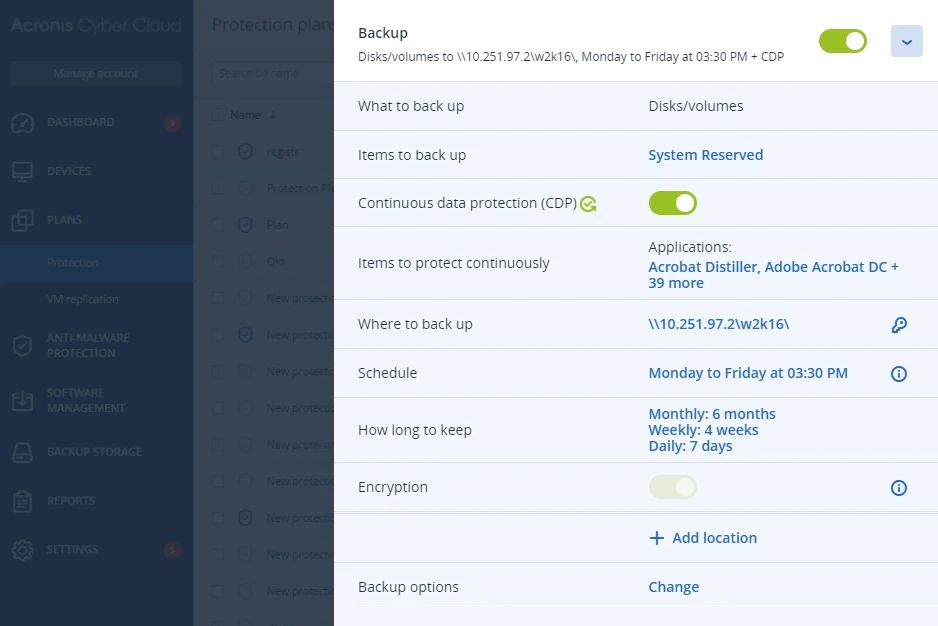
Multiple backup types
Back up disks/volumes (with all information required for the operating system to boot), individual files or folders, system states (for Microsoft Windows systems), or ESXi configurations.
Flexible backup storage options
Comply with the requirements of different clients with flexible storage options. Back up to Acronis-hosted cloud storage, public clouds such as Google Cloud Storage or Microsoft Azure, your own cloud storage, or local networked storage.
Device and port control
Strengthen data security and prevent leakage of sensitive information via local channels with granular, context-aware controls over user access to locally connected devices and ports, and data operations related to them – even for virtulized sessions.
Clipboard control
Prevent data leakage in its earliest stage by controlling data transfers between application and documents. Allow or block user access to objects of different data types copied to the clipboard, even for redirected BYOD devices in virtualized sessions.
Device control: support of encrypted removable media and screenshot capture access
Eliminate the risk of data leaks with encrypted removable media and screenshot capture control. This enables users to keep sensitive information within their organization – should a removable device get in the wrong hands or prevent screenshots from being copied to the clipboard. Keeping your clients’ sensitive data safe and secure.
Acronis Instant Restore
Cut RTOs to as little as 15 seconds with a built-in capability to restore a system by booting it as a virtual machine directly from the backup, without moving any data.
Acronis Universal Restore
Reduce the time spent on recovery tasks. Acronis Universal Restore makes recovery to dissimilar hardware faster by detecting the machine type and auto-installing appropriate drivers for the hardware.
Google Workspace data protection
Safeguard client data stored in Gmail, Drive (including Team Drives), Contacts, and Calendar by backing it up to ensure fast, reliable recovery.
Complete Microsoft 365 protection
Protect data in Microsoft Exchange Online, OneDrive for Business, Microsoft Teams and SharePoint Online with comprehensive cloud-to-cloud backup and restore.
Backup encryption
Maintain regulatory compliance and strengthen data protection by securing your backups with AES-256 data encryption for data in transit and at rest, so only you can access the data.
Deduplication
Minimize storage requirements by detecting data repetition in backups and not storing identical data more than once. Deduplication also reduces network load as duplicate data is not even transferred over the network to the backup storage.
Report scheduling
Increase visibility into information security and simplify IT security auditing with capabilities for sending scheduled reports to listed recipients in a desired format and language.
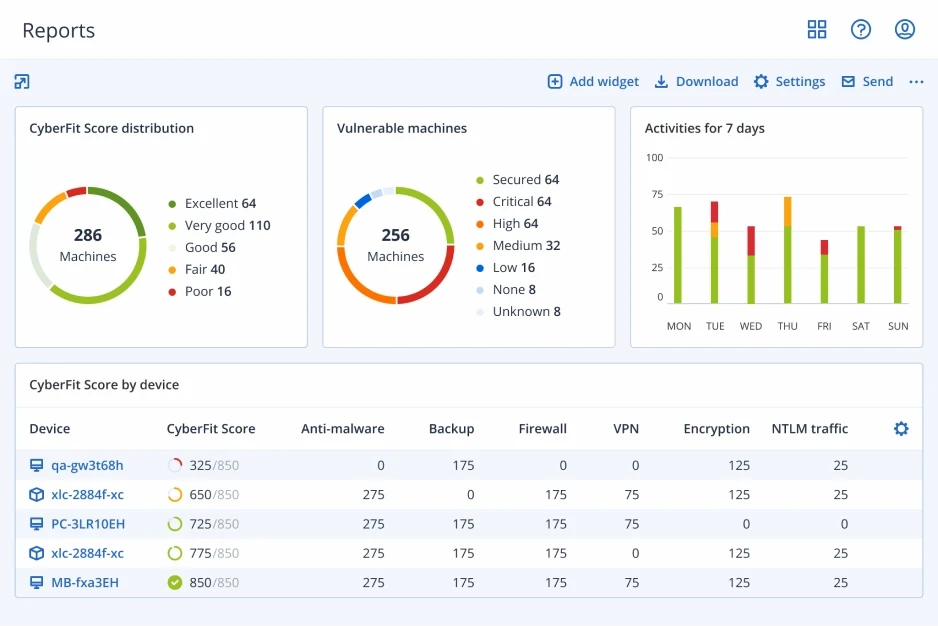
Monitoring and reporting
Simplified, at-a-glance reporting helps streamline operations while giving your technicians the insight they need to support your clients. Customize your dashboard’s widgets to view a wide range of reports – enabling you to quickly identify and remediate problems.
Centralized protection plans and group management
Ease administrative efforts with the ability to group manage multiple workloads and centralized protection plans that include all security configurations that can be applied to multiple endpoints across your client’s organization.
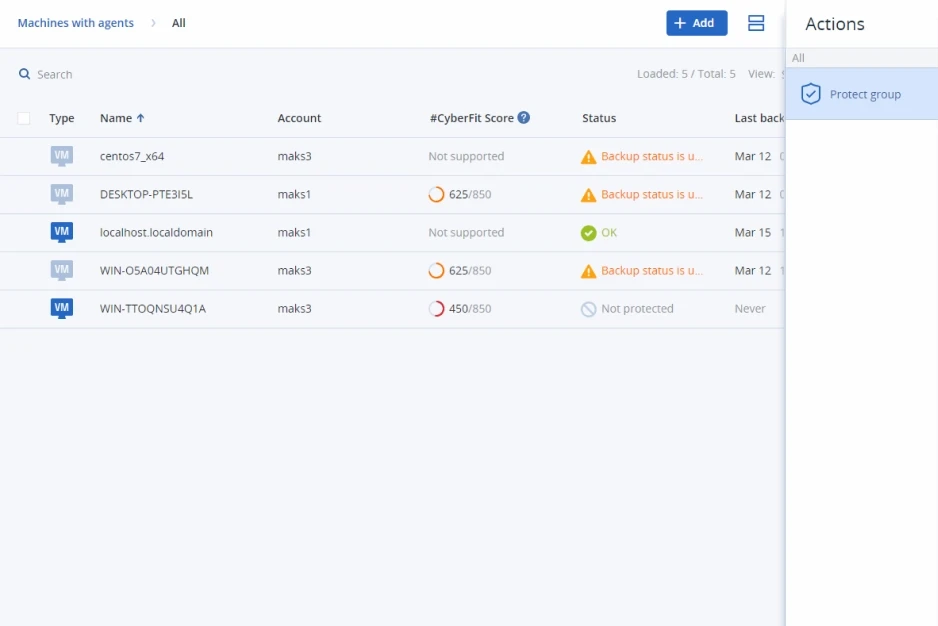
Auto discovery and remote installation
Simplify the onboarding process by installing multiple agents at once – in the cloud and on-premises. With network-based and Active Directory-based discovery, your technicians can easily install and apply protection plans remotely – helping to keep your clients safe.
Predefined protection plans
Protect your clients’ remote and office workers quickly and easily by choosing one of three preconfigured protection plans. These options save you time while ensuring you that your clients’ workloads and environments are protected.
Remote desktop assistance
Enable secure, off-site access to machines to ease remote work for users or provide technical assistance to clients with built-in remote desktop capabilities.
Hardware inventory collection
Save time and effort with an up-to-date hardware inventory. Discover all hardware assets with automatic and on-demand scans. Create hardware inventory reports, browse and filter records by multiple criteria and auto-delete them once a machine or tenant is removed.
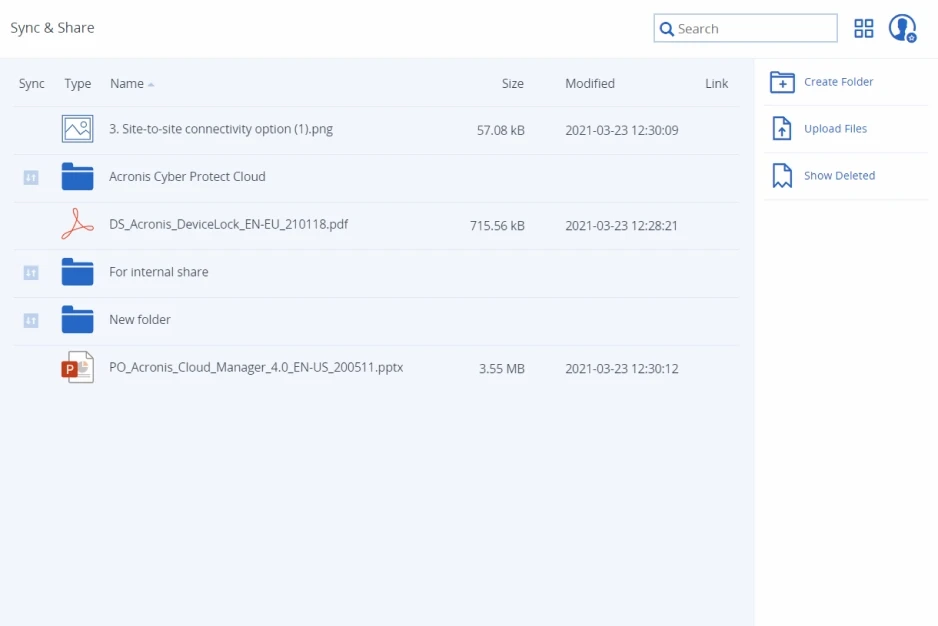
Secure file sync and share
Ensure client productivity by offering convenient, secure file sync and share capabilities. Users can securely create, edit, and share content using their own devices with pay-as-you-go pricing.
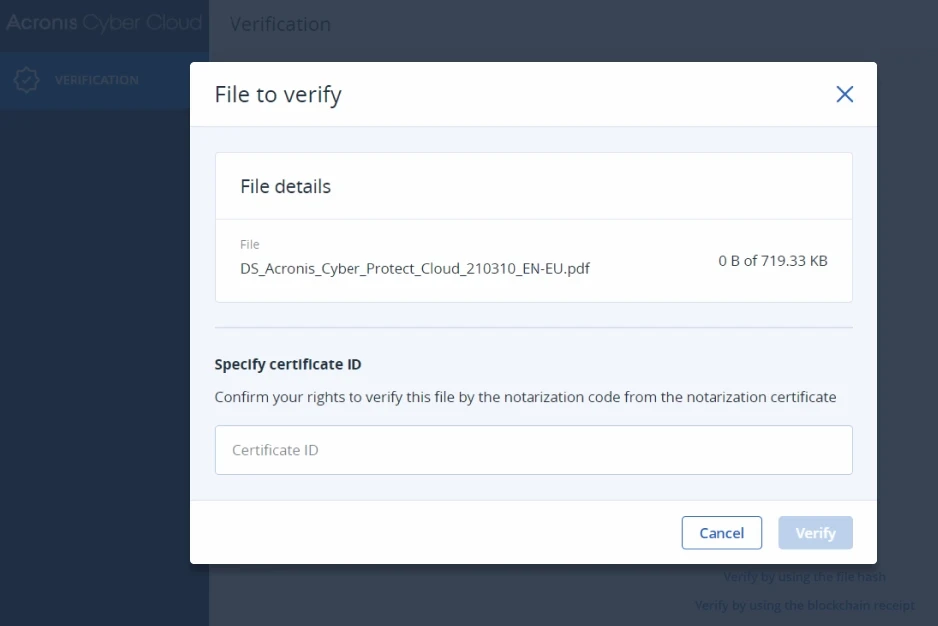
Notarization
Give clients proof of their data’s authenticity by giving them the ability to notarize any type of file, which generates a certificate with immutable, publicly verifiable proof of the file’s timestamp, integrity, and authenticity. Based on a pay-as-you-go pricing model.
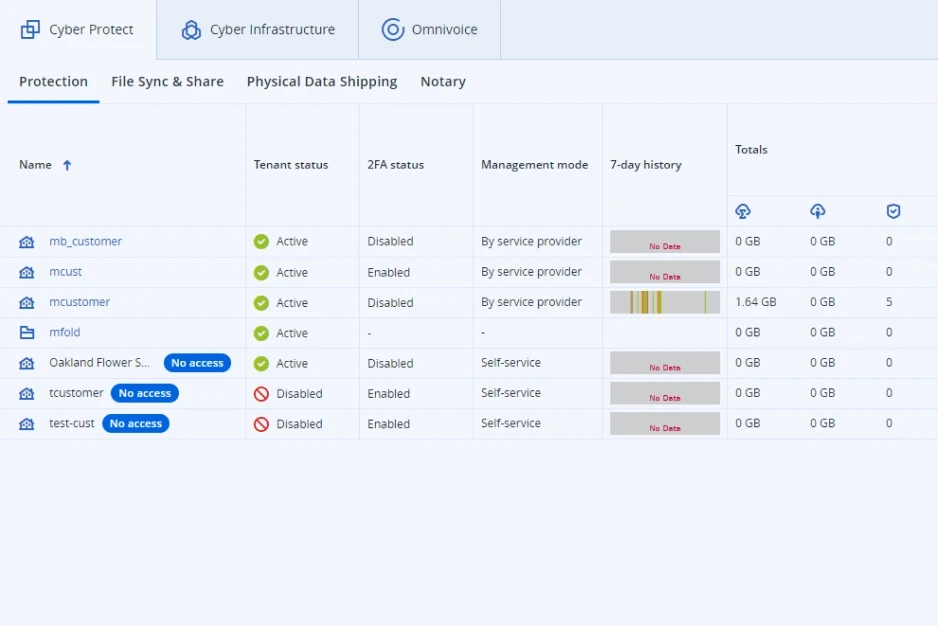
Multi-tier and multi-tenant management
Count on optimal administrative efficiency: create client or partner accounts in seconds, customize unique offerings, and manage quotas, features and administrative privileges using vertical grouping.
Electronic signing
Strengthen process compliance by allowing clients and their third parties to e-sign documents with publicly verifiable proof of the timestamp and authenticity of the signature. Based on pay-as-you-go pricing.
Test failover in isolated network environments
Verify the integrity and efficiency of disaster recovery plans by executing them via the web console in an isolated network environment, without disrupting other processes.
Point-to-site VPN connection
Enable clients to quickly and easily access files from the local site or the cloud. With the Business VPN feature, clients on DR-enabled tenants can establish a secure connection to the corporate network with their personal devices so they can access the data they need.
Firewall policies management
Easily manage firewall policies on your clients’ behalf for their disaster recovery servers through the Acronis Cyber Protect Cloud console. This enables you to simplify the support process and manage outbound and inbound firewall policies.
Straightforward pay-as-you-go pricing
Meet the dynamic needs of your clients with a 100% pay-per-use licensing model and free functionalities. Per-GB and per-seat/per-device licensing types are available.
Integration with PSA and RMM systems
Deliver services instantly using native integrations with ConnectWise (Automate, Manage, Control), Atera, Autotask, Kaseya, cPanel, HostBill, CloudBlue, Plesk, and WHMCS.
Integration with custom systems
Assimilate systems by leveraging a powerful RESTful management API or enable integration via the Acronis Cyber Backup Cloud Application Packaging Standard (APS).
Ransomware-proof backups
Ensure backups cannot be encrypted or deleted by a ransomware attack or malicious users through immutable storage, enabling you to recover quickly to the most recent clean state.
Advanced Security
Next-generation cyber protection addressing a broader scope of threats with improved detection rate and speed, smart protection plans, additional protection for backups and recovery, and forensics.
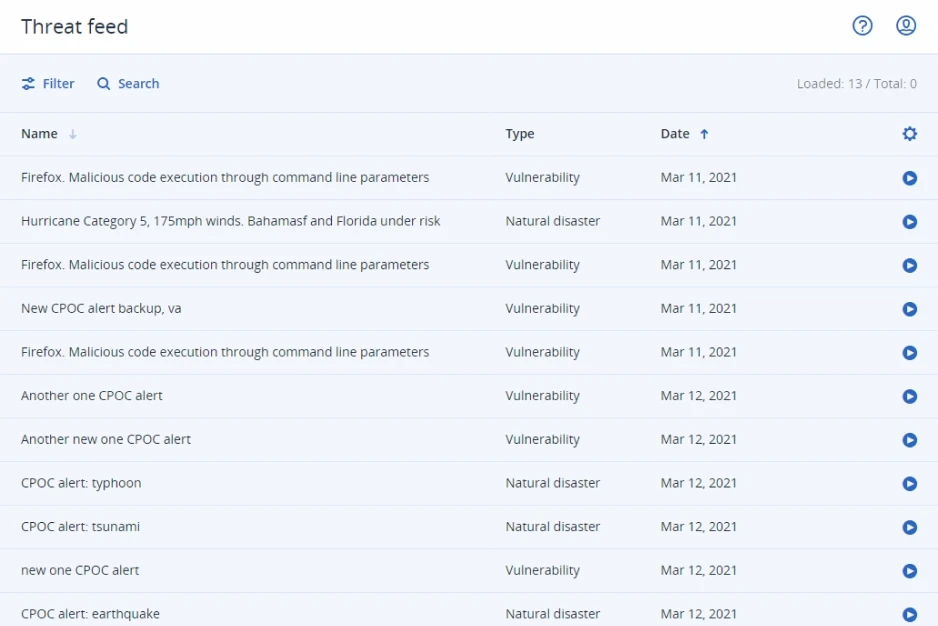
Global threat monitoring and smart alerts
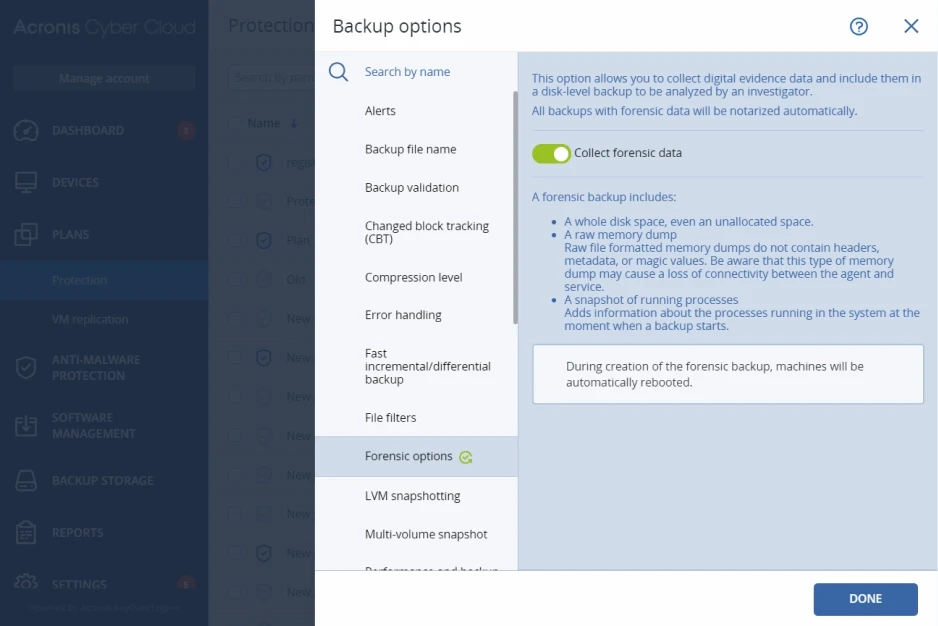
Forensic backup
Exploit prevention
Prevent advanced attack techniques, including zero-day and fileless attacks, with behavior-based detection heuristics focused on vulnerability exploitation. Acronis’ exploit prevention technology specifically detects malware that’s taking advantage of software vulnerabilities.
Enhanced signature-based detection
Increase detection rates and speed with an enhanced database of malware signatures, ensuring seamless detection of all known threats within seconds while minimizing the agent’s impact on performance.
Enhanced URL filtering
Help your clients achieve compliance and increase productivity by preventing attacks from malicious websites. Acronis URL filtering lets you control website access through an HTTP/HTTPS interceptor, manage exceptions for URLs, and perform payload analysis.
Anti-malware protection for backups
Prevent restoring infected files from backups with built-in malware scanning, including for encrypted backups. By scanning full disk backups in a centralized location, Acronis Cyber Protect Cloud helps find malware – ensuring users are restoring a backup that is clean and malware-free.
Safe recovery
Prevent dangerous infections from reoccurring with Acronis’ unique safe recovery technology. During the recovery process, the integrated solution scans the backup for malware, installs the latest security patches, and updates its antivirus databases.
Remote device wipe
Prevent business-critical data from getting into the wrong hands by remotely wiping compromised or missing Windows devices. You can protect data from being deleted by disgruntled employees or accessed from lost or stolen devices.
Global and local allowlists
Allow more aggressive behavioral heuristics with zero false positives. You can create automatic allowlist of your clients’ most used applications, including custom apps, to save time and avoid resource-draining false positives. Manual allowlisting is also supported.
Windows anti-malware management
Eliminate complexity while ensuring that Windows’ native anti-malware is properly configured. With Acronis protection plans, you can control Windows Defender Antivirus and Microsoft Security Essentials detection events, applying settings across multiple machines.
Advanced Backup
Support a wider scope of workloads with continuous protection of data, validation of backed-up data, and visibility into the protection status of assets across your clients’ IT infrastructure.
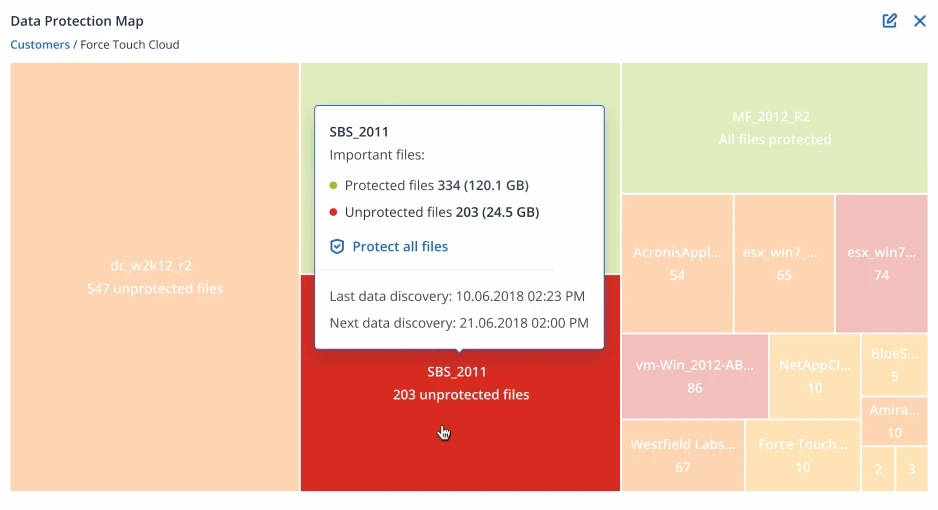
Data protection map and compliance reporting
Continuous data protection
Full or granular recovery of MariaDB and MySQL databases
During the backup of the entire workload, Acronis collects metadata for each database running on it. You can browse databases and/or fully or granularly recover data and tables without recovering the entire workload.
Application cluster backup and restore
Ease IT administrative burden with built-in capabilities for easy back up and recovery of Microsoft Exhange, Microsoft SQL Server, and Oracle DBMS Real Apllication clusters.
SAP HANA backup
Strengthen your SAP HANA database protection with consistent, script-based, disk-level backups that simplify management and do not require any SAP HANA expertise.
Off-host data processing for backup operations
Reduce the load on your clients’ workloads by moving backups replication, validation, retention and conversion into VM operations to another machine. These operations can be scheduled independently.
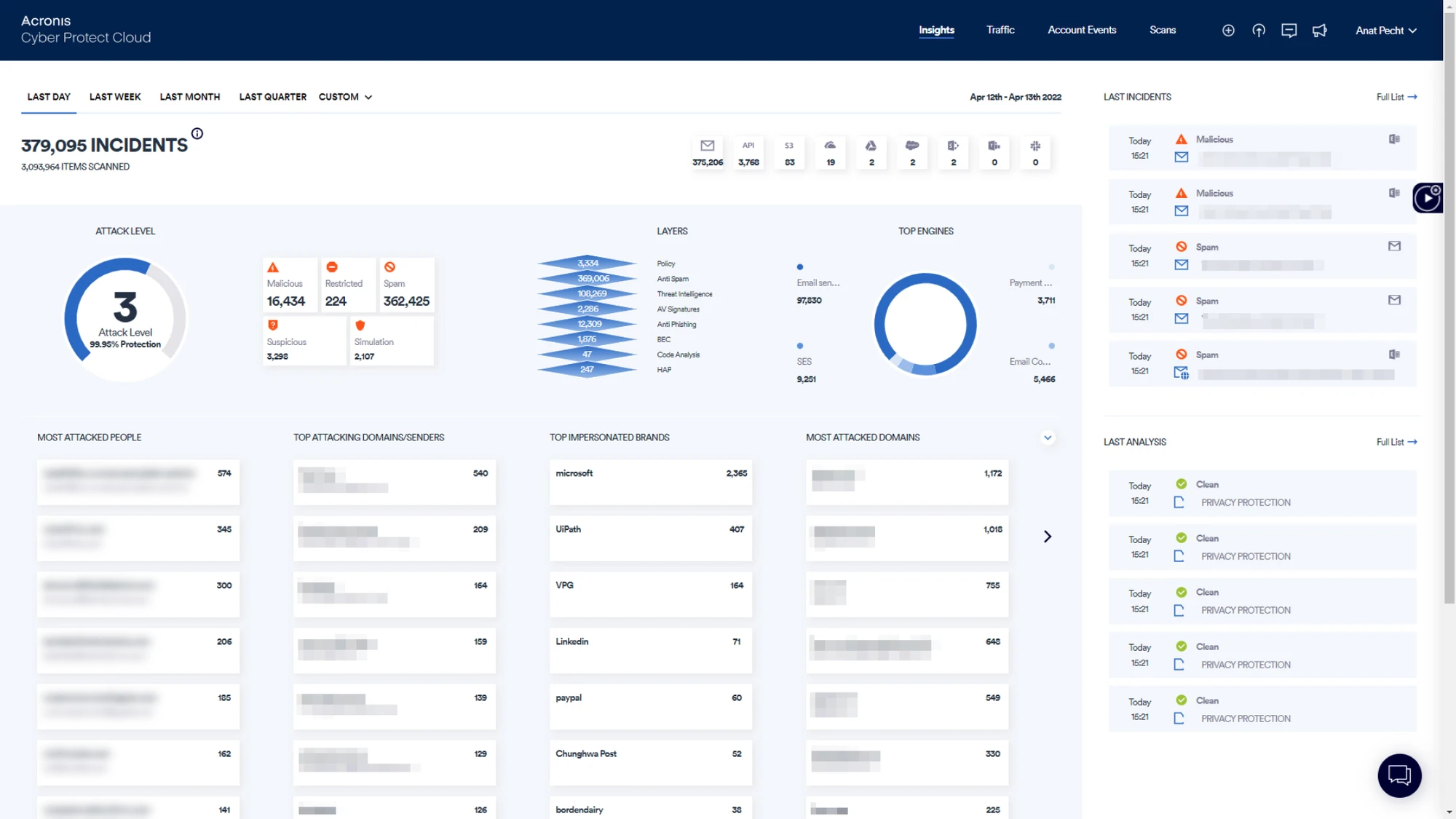
Advanced Email Security
Block any email-borne threat, including spam, phishing, business email compromise (BEC), malware, advanced persistent threats (APTs), and zero-days before it reaches end-users.
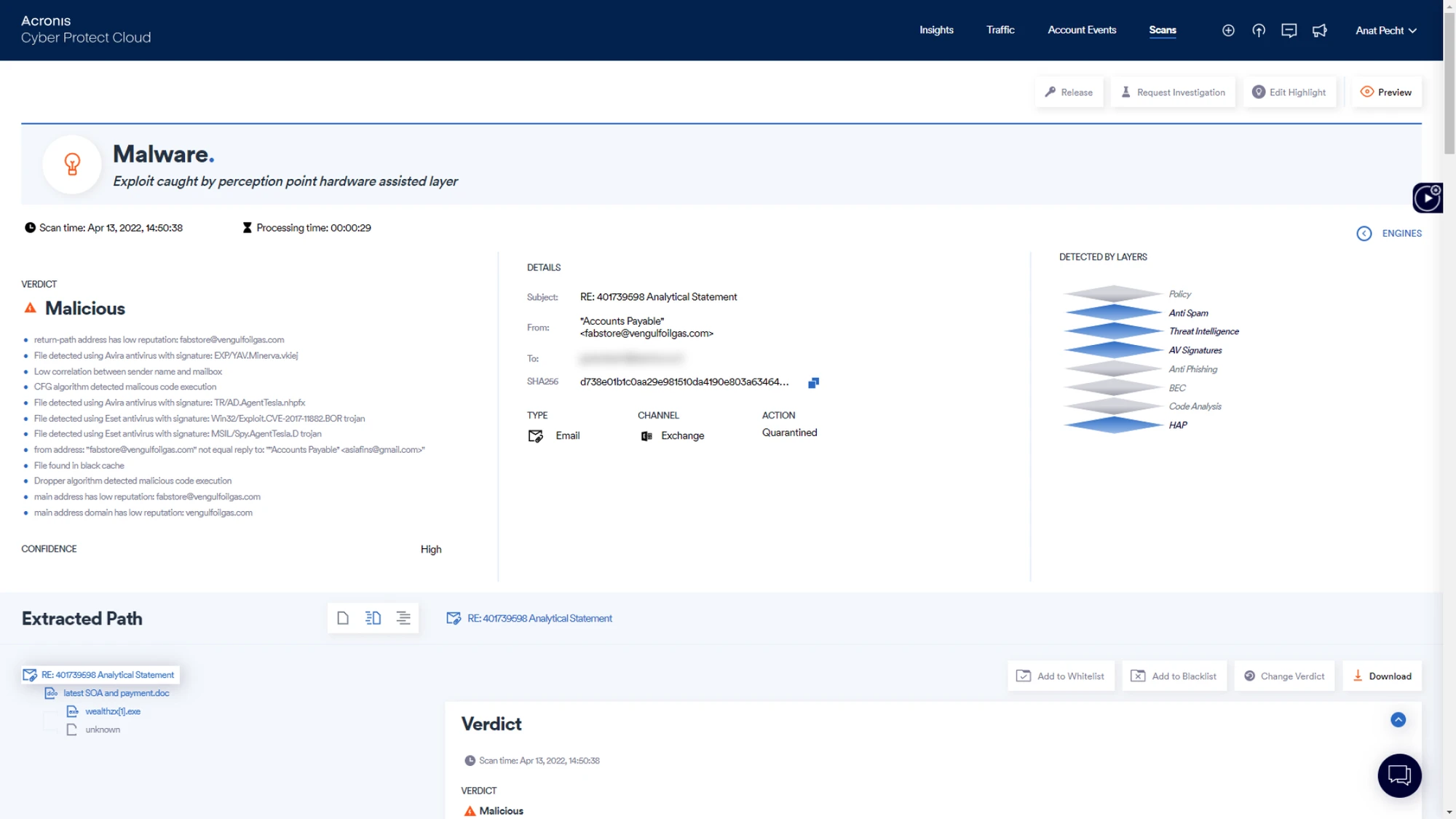
Next-generation dynamic detection
Stop zero-days and APTs with Perception Point’s unique technology – CPU-level analysis that detects and blocks advanced attacks such as APTs and zero-days at the exploit stage by identifying deviations from normal execution flow during runtime.
X-ray insights
Leverage a holistic view of the threat landscape across organizations with forensics data for each email, proactive insights on threats seen in the wild, and analysis of any file or URL on which the service delivery team needs forensics.
Spam filter
Block malicious communication with anti-spam and reputation-based filters, leveraging the combined data of several market-leading technologies.
Anti-evasion
Detect malicious hidden content by recursively unpacking the content into smaller units (files and URLs) which are then dynamically checked by multiple engines in under 30 seconds, compared to 20+ minutes for legacy, sandboxing solutions.
Threat intelligence
Stay ahead of emerging threats with the combined threat intelligence of six market-leading sources and Perception Point’s unique engine that scans URLs and files in the wild.
Static signature-based analysis
Identify known threats with best-of-breed signature-based antivirus engines enhanced with a unique tool by Perception Point to identify highly complex signatures.
Anti-phishing engines
Detect malicious URLs based on four leading URL reputation engines in combination with Perception Point’s advanced image recognition technology to validate the legitimacy of URLs.
Anti-spoofing
Prevent payload-less attacks such as spoofing, look-alike domain, and display name deception with unmatched precision through machine-learning algorithms with IP reputation, SPF, DKIM, and DMARC record checks.
Incident response service
Gain direct access to cyber analysts that act as an extension of your service delivery team, monitor all customer traffic, and analyze malicious intent with ongoing reporting and support, including handling false positives, remediating, and releasing when required.
Reporting
Demonstrate your value to customers with easily accessible and manageable datasets along with weekly, monthly, and ad-hoc reports from the Incident Response team.
Ad-hoc email analysis for end-users
Enable end-users to directly consult with Perception Point’s email security experts for suspicious emails before taking reckless action.
End-user contextual help
Flag emails with customizable banners based on policies and rules to provide end-users with additional contextual information to increase their security awareness.
Automatic email routing for Microsoft 365
Simplify the initial configuration process and speed up service provisioning by running a ready-to-use script to automatically set up routing between Microsoft 365 and Acronis.