Digital.ai Application Protection
Formerly Arxan
Our proprietary protection capabilities shield apps from reverse engineering, tampering, API exploits, and other attacks that can put your business, your customers, and your bottom line at risk.
Our proprietary protection capabilities shield apps from reverse engineering, tampering, API exploits, and other attacks that can put your business, your customers, and your bottom line at risk.
Gartner Market Guide for In-App Protection


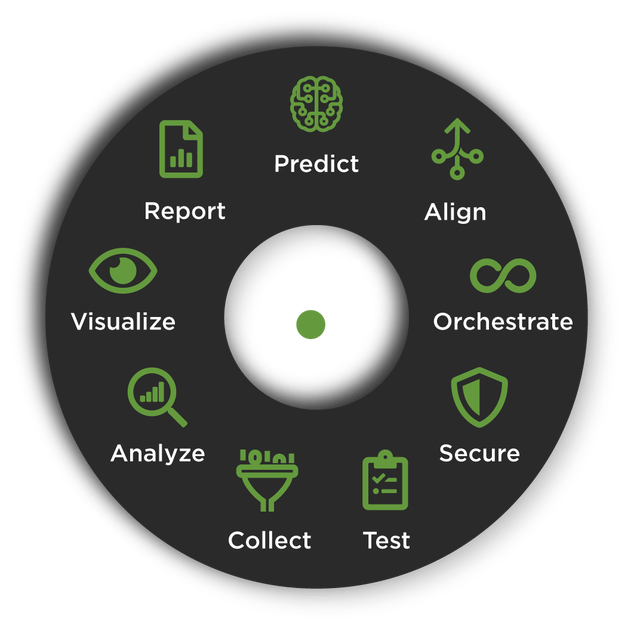
Protect apps in production against attackers intent on breaching customers and businesses. As part of the Digital.ai Platform, organizations get automated, layered, and adaptive app and data protection with real-time threat analytics, raising the alarm before damage occurs.
Comprehensive and designed to deliver real, sustained value.
Any application not properly protected – whether for mobile, desktop, or web – is at risk of being exploited by bad actors. Unprotected app vulnerabilities are impacting organizations across industries and around the world. Digital.ai commissioned research by Aite Group to assess just how widespread app vulnerabilities are.
It took an average of only 8.5 minutes to crack the apps analyzed in the study, underlying the importance of protecting applications. The following was observed – all of which can be prevented or drastically minimized with proper app security measures in place.







When addressed properly with application protection security solutions – including JavaScript protection, threat detection, and limiting API connections to known good sites, along with defensive measures that can shut down application functionality in the event of an attack – effective application security enables customers to detect and protect against active threats, shielding businesses and consumers from data breaches and financial losses.
Application hardening is a process of taking a finished application and making it more difficult to reverse engineer and tamper.
Code obfuscation is transforming a software program into code that’s difficult to disassemble and understand, but has the same functionality as the app.
Digital.ai’s application and mobile app protection solutions go beyond Runtime Application Self-Protection (RASP) by providing layered and adaptive app protection.

White-box cryptography uses encryption, obfuscation, and mathematical transformations to secure keys and critical data inside the applications running.