Advanced Backup Datasheet
PDF, 0.9 MB
Deliver near-zero RPOs and downtime with cloud backup enhancements – like continuous data protection. Save time while preventing client data loss.
Acronis delivers a unique approach by combining cloud backup with cyber protection features, such as anti-malware and antivirus – helping you keep clients’ data secure.
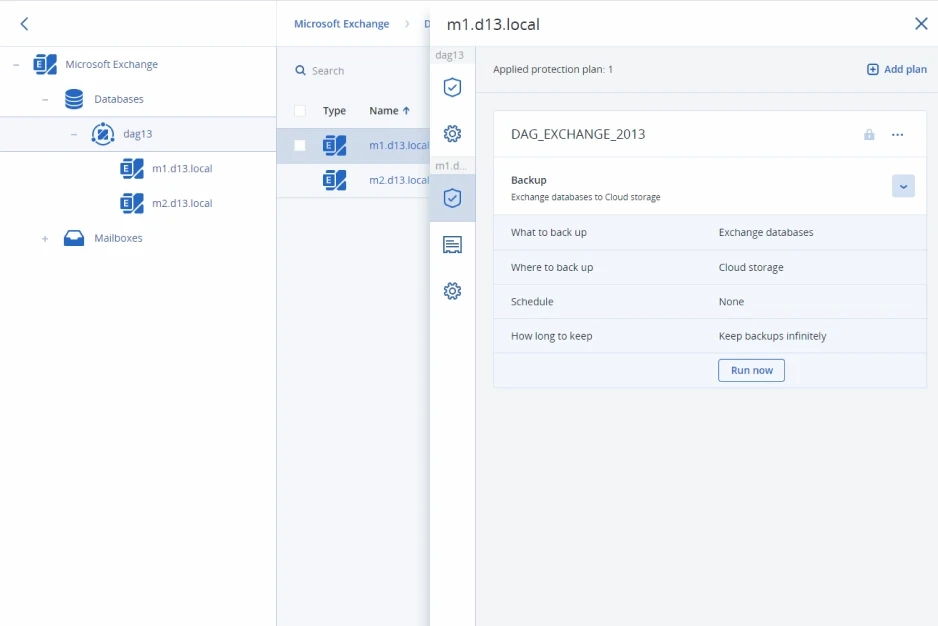
Protect more than 20 workload types from a single console, including Microsoft Exchange, Microsoft SQL Server, MariaDB, MySQL, Oracle DBMS Real Application clusters, and SAP HANA.
Benefit from backup capabilities enhanced with cyber protection – with protection with more than 20 workload types, you can protect your clients’ data confidently. Discover what backup and data protection capabilities you gain with Acronis Cyber Protect Cloud. Harness the power of one solution, one agent, and one console to deliver the comprehensive cyber protection your clients seek.
| Features | Acronis Cyber Protect Cloud |
With Advanced Backup |
|---|---|---|
| File-level, disk-level, image and application backups | ||
| Backup popular workloads like Mac, Windows, Linux, Microsoft 365, Google Workspace, Hyper-V, VMware, and much more | ||
| Hybrid storage options – Acronis-hosted storage, public clouds such as Microsoft Azure, or MSP local storage | ||
| Flexible recovery options from full systems to granular files | ||
| Cloud-Physical-Virtual migrations | ||
| Archive encryption | ||
| Incremental and differential backups | ||
| Vulnerability assessments | ||
| Extended backup support: Covers Microsoft SQL clusters, Microsoft Exchange clusters, MariaDB, MySQL, Oracle DB, and SAP HANA | ||
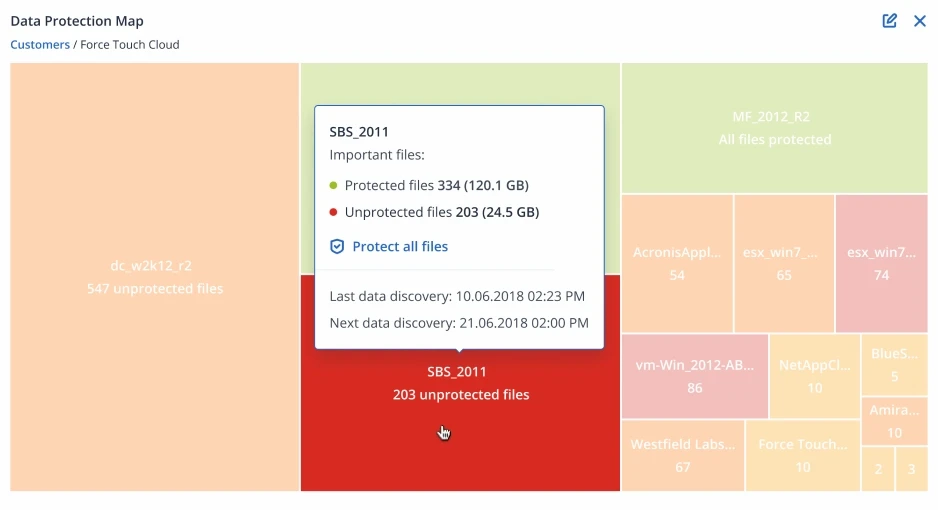
| Data protection map and compliance reporting: Scan clients’ environments to ensure their workloads, files, applications, and users are protected | ||
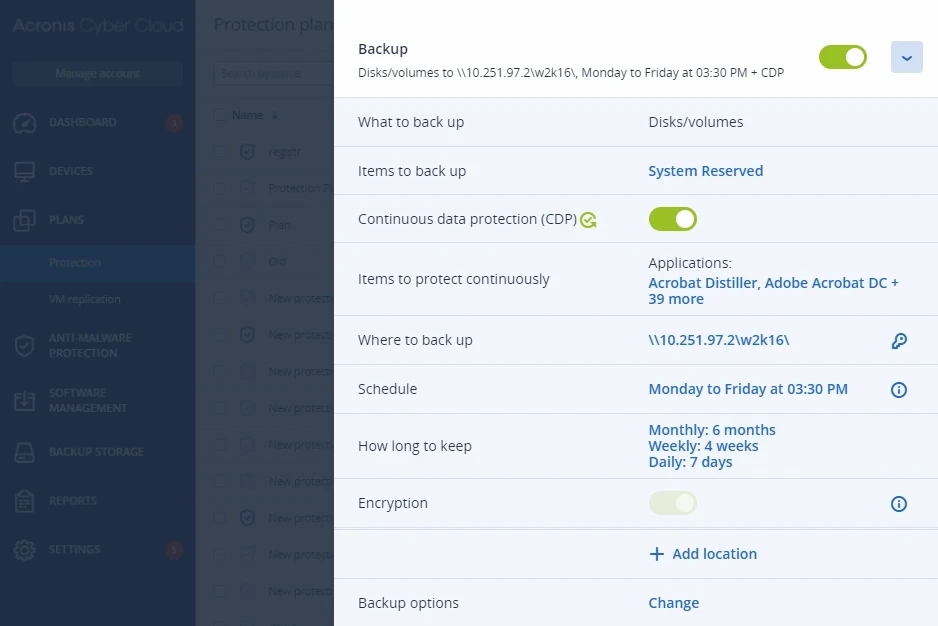
| Continuous data protection (CDP): Acronis’ agent monitors and backs up changes in real time with near-zero RPOs, ensuring no data is lost. | ||
| Off-host data processing: Reduce the CPU/RAM consumption and achieve near-zero RTO of a protected workload |
Safeguard client data, even between scheduled backups. Extend backup capabilities to SAP HANA, Oracle DB, MariaDB, MySQL, and application clusters. You’ll also have greater visibility into the protection status of all data across your clients’ infrastructure.
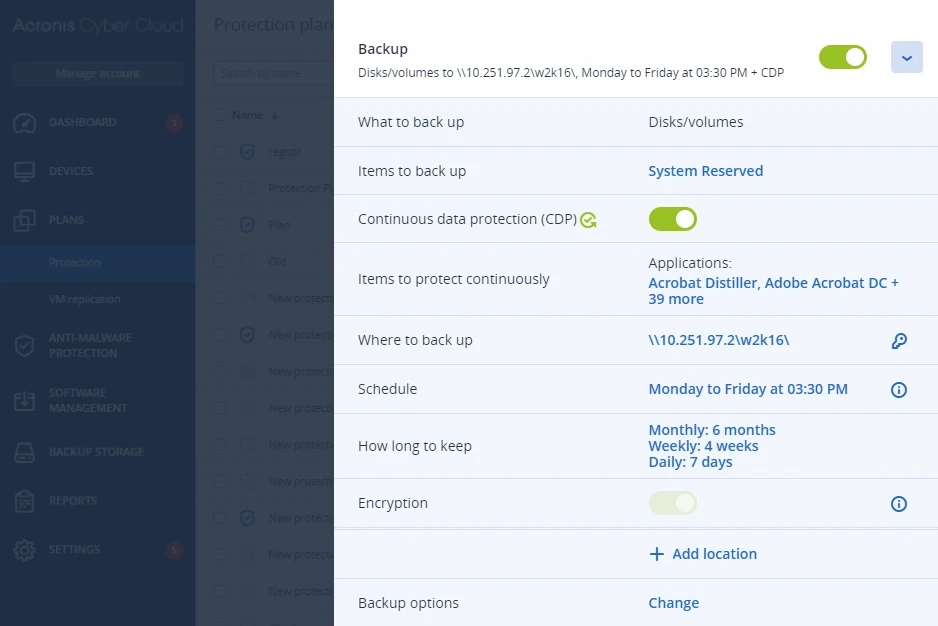
Confidently offer your clients the data protection and rapid recovery options they want and need. By adding Advanced Backup to Acronis Cyber Protect Cloud, you can eliminate downtime while simultaneously protecting clients from advanced threats. Continuous data protection captures and backs up changes made in real-time from business-critical applications so no data is lost.
Help your clients meet compliance and regulatory requirements by ensuring that all of their workloads are protected – from data to applications to systems. Acronis’ data backup software enables you to easily scan clients’ machines to identify unprotected files, applications, and workloads to proactively protect their data.
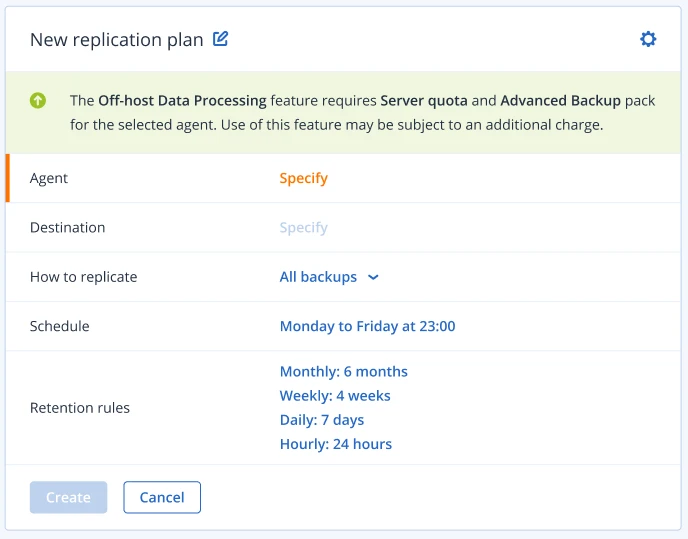
Reduce the load on your client’s workloads by moving backups replication, validation, retention and conversion into VM operations to another machine. These operations can be scheduled independently from the protection plan, e.g. on a separate schedule.
In addition to supporting Windows, Linux KVM, Mac, VMware, Hyper-V, Red Hat Virtualization, Citrix XenServer, Oracle, Microsoft 365, Google Workspace, Azure, and Amazon EC2 included in Acronis Cyber Protect Cloud, adding Advanced Backup extends that support to:
We previously used Veeam as well as legacy solutions such as local NAS. The biggest problem we had with Veeam was that it only worked well in virtual environments, and we needed many other devices and workloads protected. Acronis was fast and simple across multiple platforms including physical servers and Microsoft mailboxes.

Andrés F. Ambrosi Chica
ICT Advisory Manager, AMBROSS-TI
![]()
Get a seamless hybrid experience and ensure ultimate data safety and accessibility by backing up and recovering customers’ systems, applications, and data via both local and cloud storage. Oversee all clients from a single pane of glass with management components centrally located in the Acronis Cloud.

Guarantee that critical data is protected for compliance reporting, with the data protection map. Use the automatic data classification to track the protection status of important files, folders, and workstations. If they are not protected, an alert is created so you can protect your clients’ critical data.
Ease the IT administrative burden with built-in capabilities to easily backup and restore Microsoft Exchange, Microsoft SQL Server, and Oracle DBMS Real Application clusters. This easy to preform backup for service providers helps you quickly and easily protect multiple workload with one solution.
Strengthen SAP HANA database protection with consistent, script-based, disk-level backups that simplify management and do not require any SAP HANA expertise. If a recovery is needed, you can perform image-based backup for your clients’ SAP HANA database and all the data associated with it, including application configurations.
Add other powerful components to strengthen your services even further with advanced protection packs and unique cyber protection capabilities. Control your costs by paying only for the functionalities your clients need.
Advanced packs include:
Enhance your security services with integrated cyber protection that includes full-stack anti-malware. Increase your detection rate and responsiveness to the latest cyberthreats. Extend cyber protection to web browsing, backed-up data, the recovery process, and exploit prevention. Enable investigations by capturing forensic data in backups.
Defend clients’ data, even between scheduled backups. Extend backup capabilities to SAP HANA, Oracle DB, MariaDB, MySQL, and application clusters. You can also gain visibility into data-protection statuses across your clients’ infrastructure.
Block any email threat, including spam, phishing, business email compromise (BEC), advanced persistent threats (APTs), and zero-days in seconds before it reaches end-users. Leverage Perception Point’s next-generation technology for lightning-fast detection and easy deployment, configuration, and management.